Closing: May 23, 2024
6 days remainingPublished: May 3, 2024 (14 days ago)
Job Requirements
Education:

Work experience:

Language skills:

Job Summary
Contract Type:

Sign up to view job details.
Qualifications
- Bachelor’s and / or Advanced degree in Computer Science or any related disciplines. Professional certifications such as CISA, ISO27001, CISSP, CISM, CEH, will be an asset.
- 9+ years relevant experience in Information Security, IT Control and IT Risk.
- Hands-on experience in security systems review, Acunetix, Windows Server, Linux server, SIEM, Nipper, Nessus.
- Demonstrable experience with change management, user access management, segregation of duties matrix, and incident response.
- Thorough understanding of the latest security principles, techniques, and protocol
Responsibilities
Qualifications
- Bachelor’s and / or Advanced degree in Computer Science or any related disciplines. Professional certifications such as CISA, ISO27001, CISSP, CISM, CEH, will be an asset.
- 9+ years relevant experience in Information Security, IT Control and IT Risk.
- Hands-on experience in security systems review, Acunetix, Windows Server, Linux server, SIEM, Nipper, Nessus.
- Demonstrable experience with change management, user access management, segregation of duties matrix, and incident response.
- Thorough understanding of the latest security principles, techniques, and protocol
- Lead the IT security team in line with best practice such as ISO27001
- Identify potential threats to the confidentiality, integrity and availability of the company’s systems and network.
- Identify appropriate security technologies based on risks, policies, and architecture.
- Support the IT Architecture Review process and evaluate associated security of the proposed architectures.
- Contribute towards establishing credible security awareness throughout the organization.
- Create and establish processes around vulnerability management.
- Plan, buy, and roll out security hardware and software, ensuring IT and network infrastructure is designed according to best security practices.
- Perform real-time analyses of immediate threats.
- Triage when security threats materialize.
- Keep abreast of developing security threats and assist management to understand potential security problems that may arise from acquisitions or other big business moves.
- Prevent staff from misusing or misappropriating data.
- Ensure that only authorized users have access to restricted data and systems.
- Keep ahead of security needs by implementing programs or projects that mitigate risks, e.g. regular system patches.
- Determine root causes of breaches and deal with those responsible if internal while also planning to avoid repeats in future.
- Ensure IT security baselines and considerations are embedded in the procurement process for all applications.
- Keep informed of industry trends in cyber-security.
- Drive purchase of security solutions to combat IT security risk.
- Perform other tasks and duties as assigned by the Director, ITSSC.
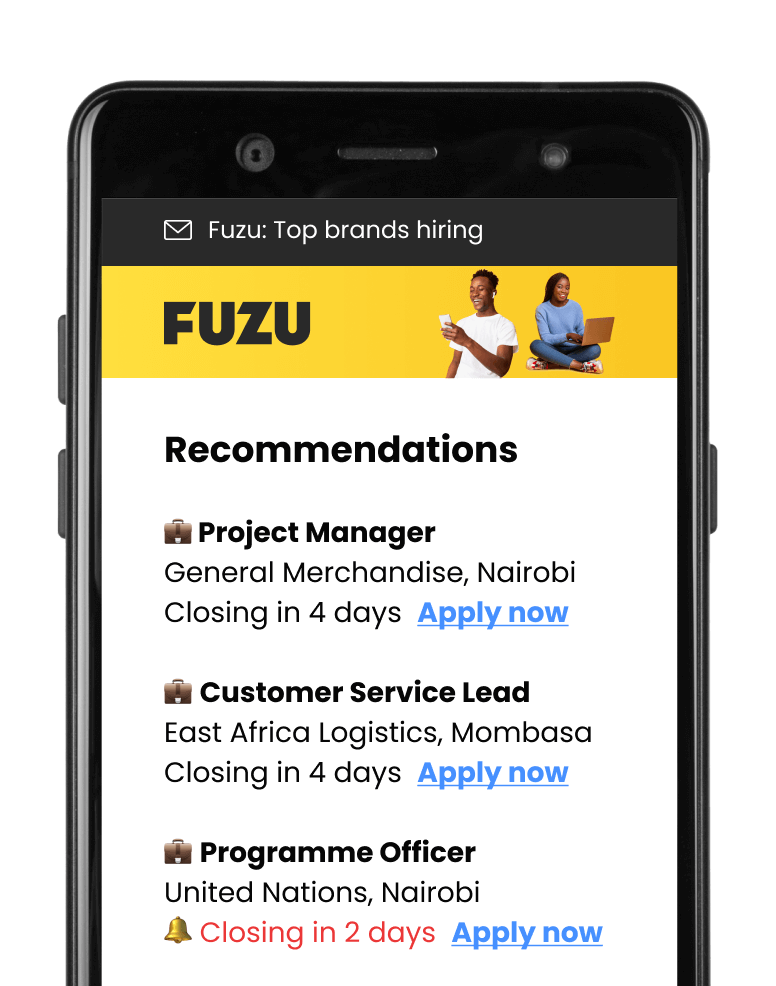
Applications submitted via Fuzu have 32% higher chance of getting shortlisted.