Closing: Apr 8, 2024
This position has expiredPublished: Apr 5, 2024 (28 days ago)
Job Requirements
Education:

Work experience:

Language skills:

Job Summary
Contract Type:

Sign up to view job details.
Qualification (Minimum)
- Bachelor’s degree in computer science/information technology or any other related field from a recognized university
- Minimum3 years’ experience
- Excellent communication, analytical and interpersonal skills.
- Ability to work with minimal supervision over long hours when addressing system issues.
- Sound ability to prioritize, time-manage and fast in decision-making.
Responsibilities
Qualification (Minimum)
- Bachelor’s degree in computer science/information technology or any other related field from a recognized university
- Minimum3 years’ experience
- Excellent communication, analytical and interpersonal skills.
- Ability to work with minimal supervision over long hours when addressing system issues.
- Sound ability to prioritize, time-manage and fast in decision-making.
- Implementation of the organizations cyber security strategy.
- Perform system risk assessments for all solutions being delivered and facilitate the reporting of findings, formulation, and logging of management actions, and tracking and reporting of remediation efforts.
- Ensure that change and incident management procedures are implemented and report on gaps noted for remediation.
- Provide training and awareness to facilitate the embedment of secure coding standards, tools and processes within the development teams.
- Ensure that the IT infrastructure and applications have adequate defense in depth controls put in place.
- Review and ensure that all open issues identified by risk team, IT security applications and auditors are closed within the agreed time frame.
- Keep up to date with, and understand, relevant laws and regulations such as data privacy laws
- Participate in and provide QA for UAT and SIT testing.
- Ensure that all systems undergo a pretest prior to go live.
- Ensure that staff members are adequately trained on cyber security issues.
- Ensure that the organization has adequate IT DR measures in place.
- Performs process-level walkthroughs, control testing, etc. for the identification and assessment of IT risks and controls.
- Undertaking risk reviews of the IT control framework
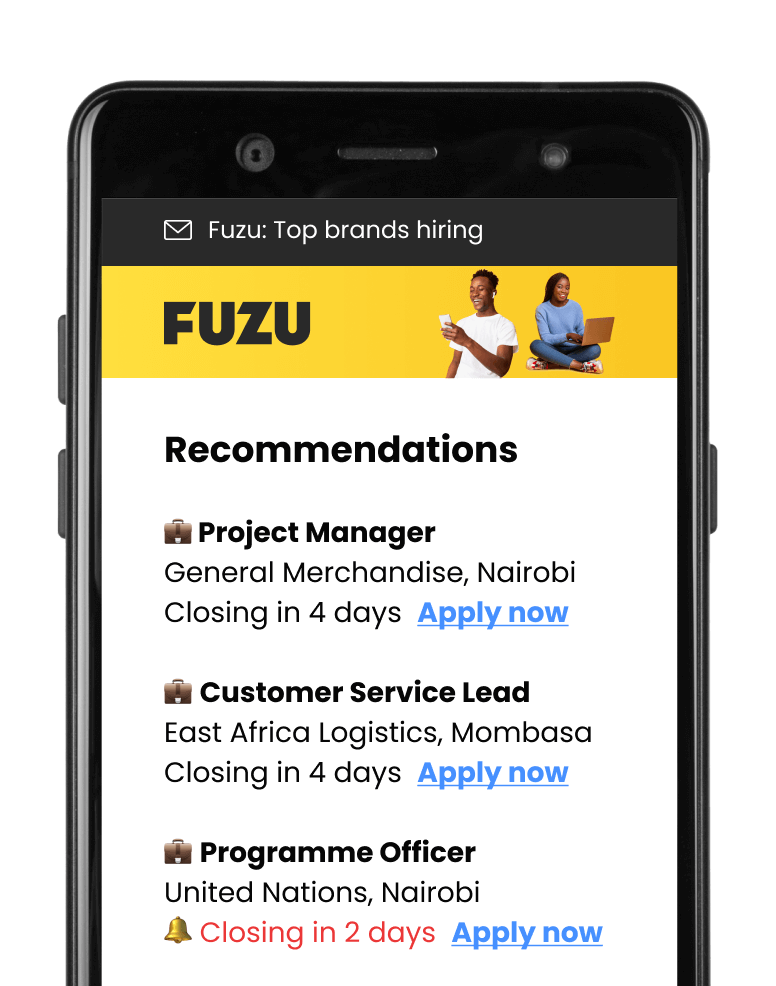
Applications submitted via Fuzu have 32% higher chance of getting shortlisted.