Closing: May 2, 2024
3 days remainingPublished: Apr 15, 2024 (15 days ago)
Job Requirements
Education:

Work experience:

Language skills:

Job Summary
Contract Type:

Sign up to view job details.
Person Specifications
For appointment to this grade, a candidate must have: -
- Bachelor's degree in computer science, Information Technology, or equivalent qualification from a recognized Institution;
- Minimum KCSE C+ (plus) or its equivalent from a recognized Institution;
- Relevant certifications (e.g., CISA, CISSP, CISM, CompTIA Security+, etc.) will be an added advantage;
- Proficiency in usage of security tools and technologies, such as firewalls, intrusion detection systems, and vulnerability management tools; and
- Fulfilled the requirements of Chapter Six of the Constitution.
Responsibilities
Person Specifications
For appointment to this grade, a candidate must have: -
- Bachelor's degree in computer science, Information Technology, or equivalent qualification from a recognized Institution;
- Minimum KCSE C+ (plus) or its equivalent from a recognized Institution;
- Relevant certifications (e.g., CISA, CISSP, CISM, CompTIA Security+, etc.) will be an added advantage;
- Proficiency in usage of security tools and technologies, such as firewalls, intrusion detection systems, and vulnerability management tools; and
- Fulfilled the requirements of Chapter Six of the Constitution.
The duties and responsibilities of the officers will entail: -
- Maintaining an updated IT Security Manual;
- Regularly verifying operating systems on company clients and servers (both on- premises and in the cloud) are up to date;
- Conducting risk assessments to identify potential security threats and vulnerabilities; Implementing strategies to mitigate risks and enhance overall security posture; Defining and enforcing security policies and procedures across the organization; Ensuring compliance with industry standards and legal requirements; Establishing an incident response plan to handle security incidents effectively; Investigating and responding to security breaches, unauthorized access, and data breaches;
- Conducting regular training sessions to enhance security awareness;
- Implementing strong authentication mechanisms (e.g., multi-factor authentication); Addressing findings and recommendations from audits;
- Monitoring network traffic, logs, and security events and generating regular security reports for management;
- Evaluating the security practices of third-party vendors and service providers;
- Collaborating with teams to develop disaster recovery and business continuity plans;
- Implementing encryption protocols to protect sensitive data; and
- Ensuring data privacy and compliance with relevant regulations.
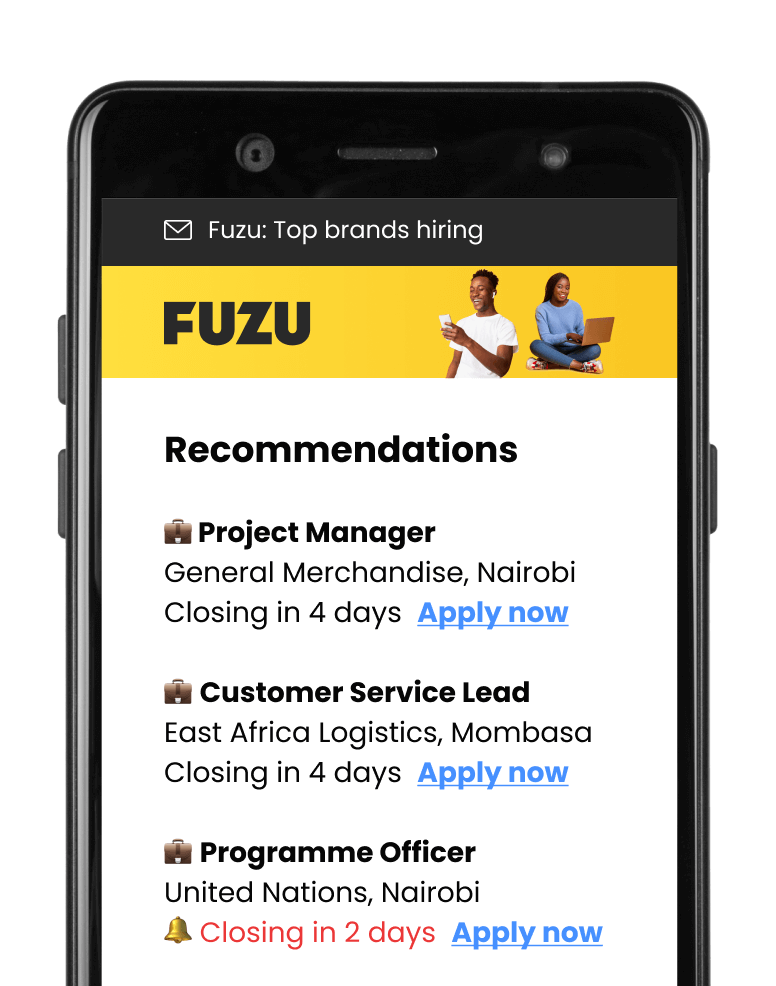
Applications submitted via Fuzu have 32% higher chance of getting shortlisted.