Closing: May 9, 2024
5 days remainingPublished: Apr 24, 2024 (10 days ago)
Job Requirements
Education:

Work experience:

Language skills:

Job Summary
Contract Type:

Sign up to view job details.
Qualifications and Experience
- Bachelor's Degree in Computer Science, Information Technology, Accounting, or related field. Masters degree and professional certifications such as Security+, CISA, CISM, CISSP, ISO 27001 are added advantages.
- 2-5 years experience as an IT Auditor, IT Control Officer, or administering Users and Administrators access controls in banking, finance, insurance industries. .
Competencies:
- Excellent analytical and problem-solving skills.
- An excellent team player with strong communication and interpersonal skills.
- Excellent time management skills
- Pay excellent attention to details
- Knowledge of banking or FinTech industry regulations or standards.
Responsibilities
Qualifications and Experience
- Bachelor's Degree in Computer Science, Information Technology, Accounting, or related field. Masters degree and professional certifications such as Security+, CISA, CISM, CISSP, ISO 27001 are added advantages.
- 2-5 years experience as an IT Auditor, IT Control Officer, or administering Users and Administrators access controls in banking, finance, insurance industries. .
Competencies:
- Excellent analytical and problem-solving skills.
- An excellent team player with strong communication and interpersonal skills.
- Excellent time management skills
- Pay excellent attention to details
- Knowledge of banking or FinTech industry regulations or standards.
- The Access Control Officer will work with the guidance of the Lead, IT & E-Business Control to manage Users’ and Administrators’ accesses to IT systems in line with the organization’s access control policy.
- The Access Control team will work closely with the Information Security Team and other teams to prevent access breaches across the enterprise.
Duties
The Access Control Officer will:
- Assist in defining and enforcing access control policies and entitlements.
- Administer user permissions on IT systems, applications, databases, and data including onboarding (provisioning) based on the principle of least privilege, and offboarding (de-provisioning) of users on systems.
- Administer Identity and Access Management (IAM) tools, Multi-Factor Authentication (MFA) solutions, etc. to enhance the organization's security posture.
- Monitor compliance with policies, and regulations, for staff access to systems, applications, databases, and data.
- Review/investigate access control breaches and recommend corrective actions.
- Work closely with system administrators, application owners, and security teams to resolve issues.
- Collaborate with vendor(s) to resolve access issues on solutions.
- Work with business leaders and product leaders to ensure that roles and permissions meet the needs of the business and comply with relevant laws and regulations.
- Respond to audit findings and implement remediation measures.
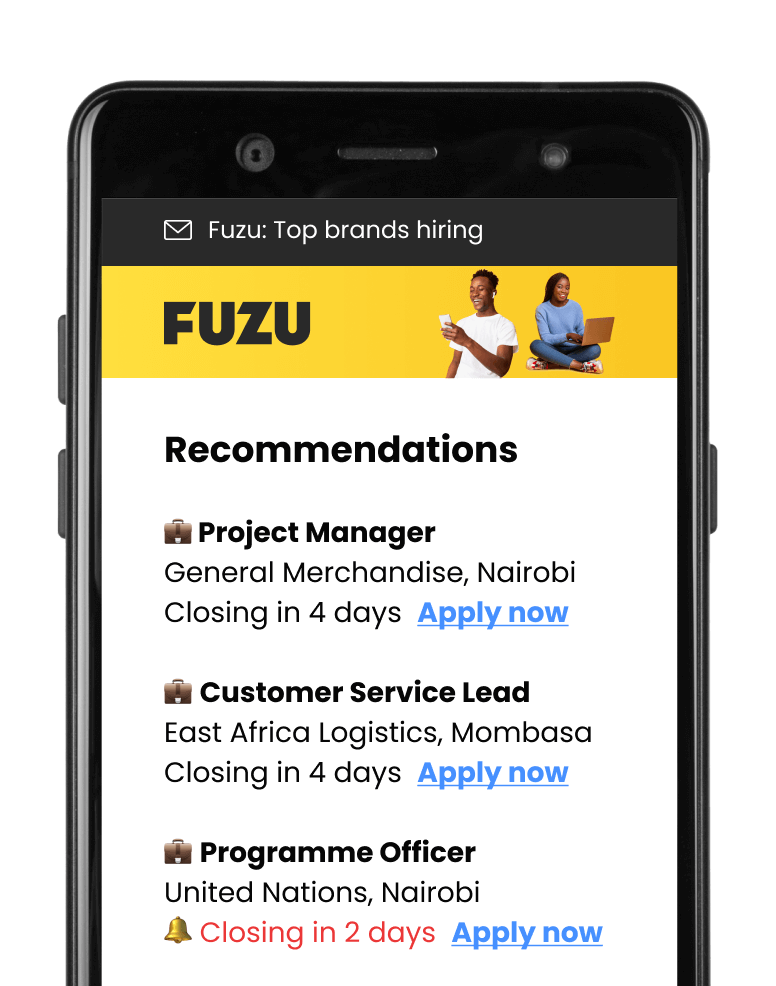
Applications submitted via Fuzu have 32% higher chance of getting shortlisted.